WEB APPLICATION DEVELOPMENT
We walk the extra mile to develop your web apps that are well-planned, highly scalable, and secure. A proud web application development company.
Software On-Demand. How we do it?
Backend development: ‘Behind-the-scenes’ functionality of web applications
With 10+ years of experience, we specialize in developing backend systems using microservices-based architecture. We factor in the aspects of multi-tenancy, scalability, self-service/automation, third-party integration, reporting, and business metrics. By evaluating these factors, we aim to deliver flawless functional apps, top-class tech stack, including the best programming language for web application development software.
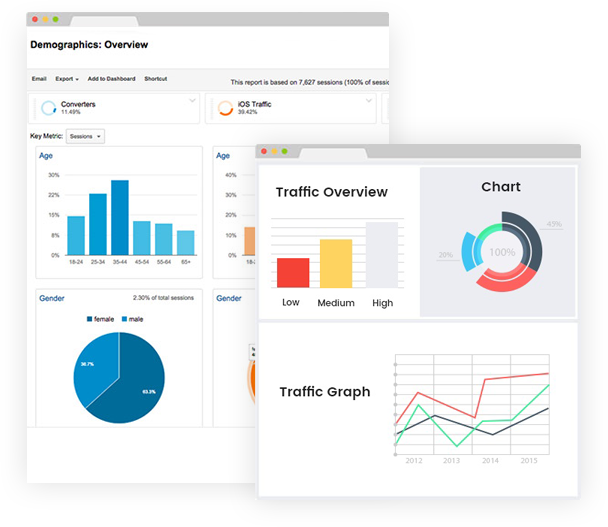

CHECK YOUR WEBSITE SEO SCORE
How Your Website Is Performing?
What we do and what we offer
We provide marketing services to startups and small businesses looking for a partner for their digital media. We work with you, not for you. We are on a mission to build, grow and maintain loyal communities. Cras mattis iudicium purus sit amet fermentum at nos hinc posthac, sitientis piros afros lorem consectetur viverra.
Do You Want More SEO Traffic?
Our team of experts can optimize your website for search engine. Lorem ipsum dolor sit amet, consectetur adipiscing elitphasellus lorem.
Front-end development: Clean scripting and a delightful UX
Change is the only constant. So, our engineers constantly hone their skills in improving UI implementation and ensure impeccable product quality. Over 10 years of expertise in building great UX and exhibiting special effects through JavaScript, allow us to add wow factors that are beyond user expectation for every web app we develop.
How we secure your web your application: No half measures
TACKLING WEB APPLICATION VULNERABILITIES
Typically vulnerabilities are the result of a lack of input/output sanitization enabling the use of potential attack vectors including:
SQL Injection
A code injection technique to manipulate the database to reveal any sensitive information
Cross-site Scripting (XSS)
The attacker injects scripts activating Trojans, targeting a user to access accounts or altering page content
Remote File Inclusion
An attack to remotely inject a file in the web application server executing malicious scripts
Cross-site Request Forgery
An attack resulting in an unsolicited transfer of funds, change of passwords or data theft
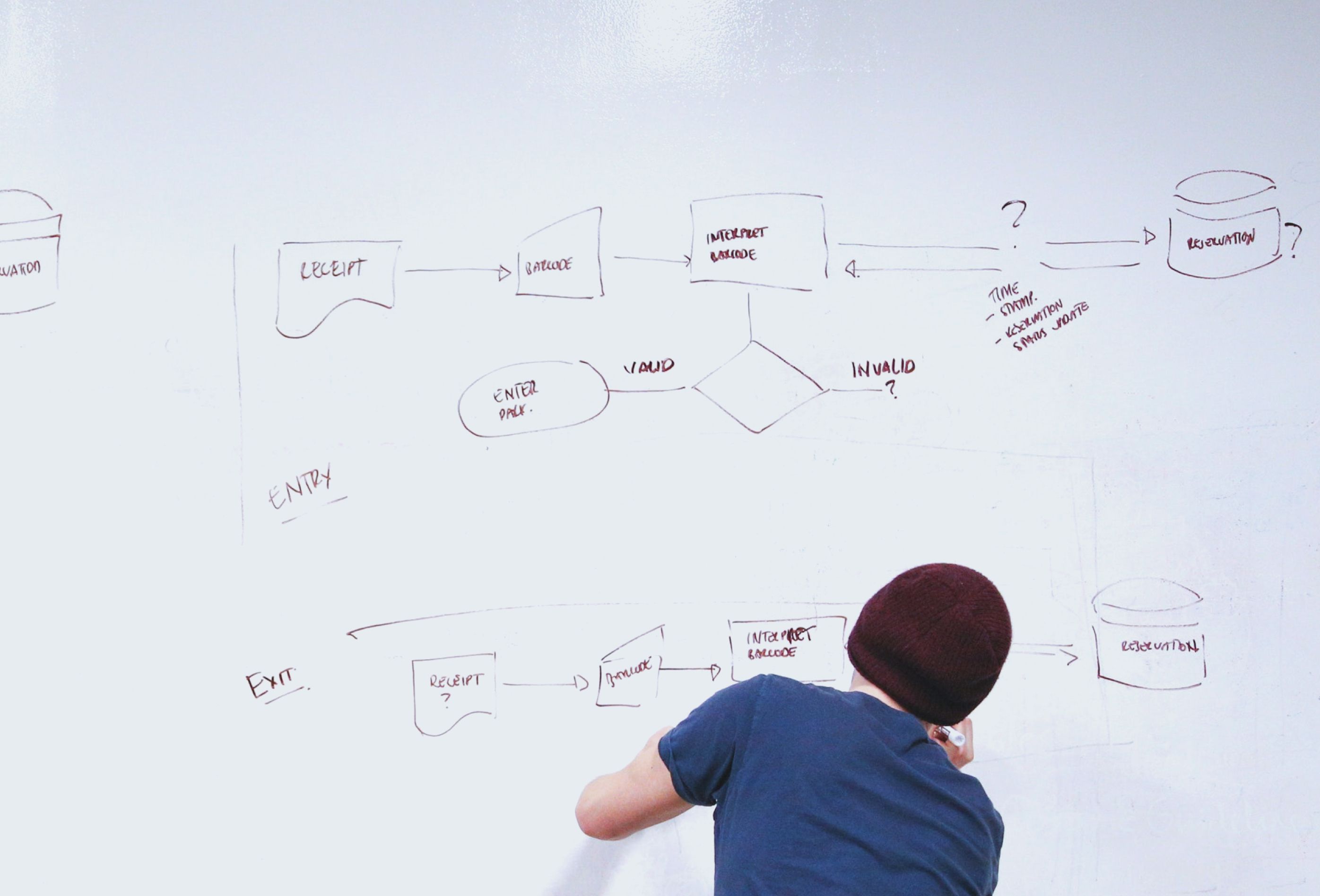
Translate your value proposition to the product roadmap
A roadmap is a strategic-level blueprint for converting your value proposition into a product. Think about your roadmap and milestones, not just in terms of feature list but from customer value stand-point. A few minutes of research based on the data gathered on your target audiences’ persona help you prioritize features and fixes.
The process is defined as a sequence of steps. When followed, it helps to achieve a goal. We consider it - the art of thinking through.
From a naive business idea on a scribble pad to a solid document articulating feature scoping, use cases and milestone definition, we lay out the scope of your project along with your collaboration. And this helps in making lesser mistakes in the journey. This makes clients trust us one of the leading startup consulting firms globally.